The Complete Corporate Cybersecurity Training for Modern Businesses
Boost your company's security posture without hiring an expensive consulting firm.
Identify Vulnerabilities, Harden Systems, and Build a Resilient Security Strategy
CLICK BELOW TO WATCH FIRST!

4.9/5 star reviews
Thousands of happy customers worldwide
AS SEEN ON
Learn Why Strengthening Your Company's Security Posture Is Non-Negotiable
Does this sound like you?
Leaving critical systems exposed to common attacks.
Unclear on how to configure firewalls and access controls correctly.
Employees frequently fall for phishing scams.
Unsure which security tools are worth the investment.
Difficulty proving compliance to auditors and clients.
Deploy our proven Defense-in-Depth framework.
Set up effective network segmentation and zero-trust access.
Use our incident response templates to act within minutes.
Invest only in vetted security tools that fit your environment.
Build metrics that demonstrate ROI and maturity to leadership.
What You Will Get in This Course

Cybersecurity Fundamentals
Understand core security concepts, today’s threat landscape, and compliance drivers.

Network Defense Essentials
Configure firewalls, IDS/IPS, and network segmentation to block attacks.

Endpoint Hardening
Implement patch management, EDR, and secure configurations on every endpoint.

Identity & Access Management
Apply least privilege, MFA, and role-based access controls across the enterprise.

Secure Application Practices
Spot and mitigate the OWASP Top 10 vulnerabilities in your applications.

Incident Response & Forensics
Create playbooks, triage alerts, and collect evidence during incidents.
TESTIMONIALS
What our students are saying...

" We closed 85% of our audit findings in just a month. The practical demos were invaluable! "
- James Wu


" Our small team now confidently handles security incidents without outsourcing. The step-by-step labs made all the difference. "
- John Doe


" I passed the Security+ exam on my first try and immediately improved our patch management process. Highly recommended. "
- Roberta Johnson

MODULES
FOLLOW MY STEP BY STEP VIDEO TRAINING
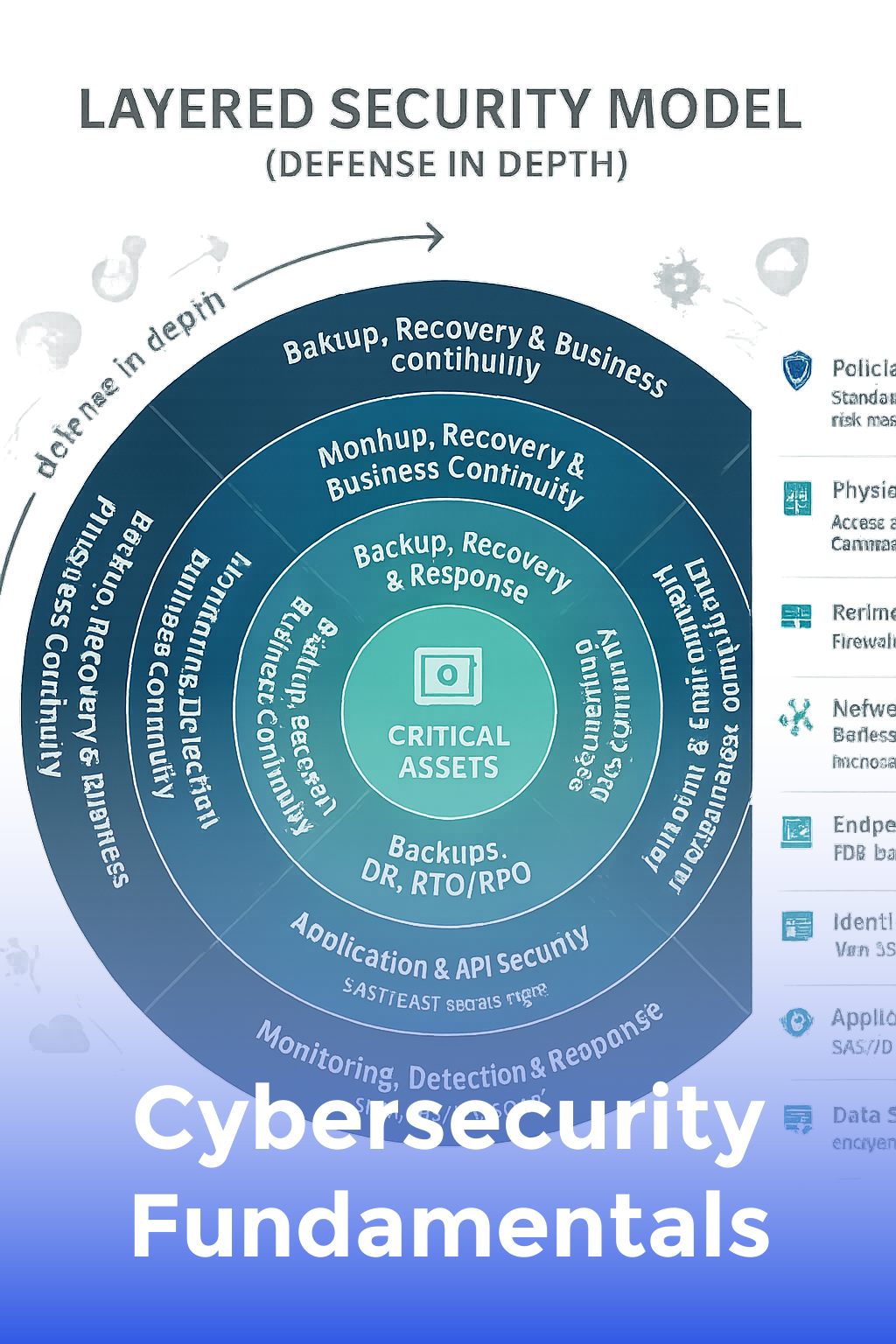
Cybersecurity Fundamentals
Understand core security concepts, today’s threat landscape, and compliance drivers.
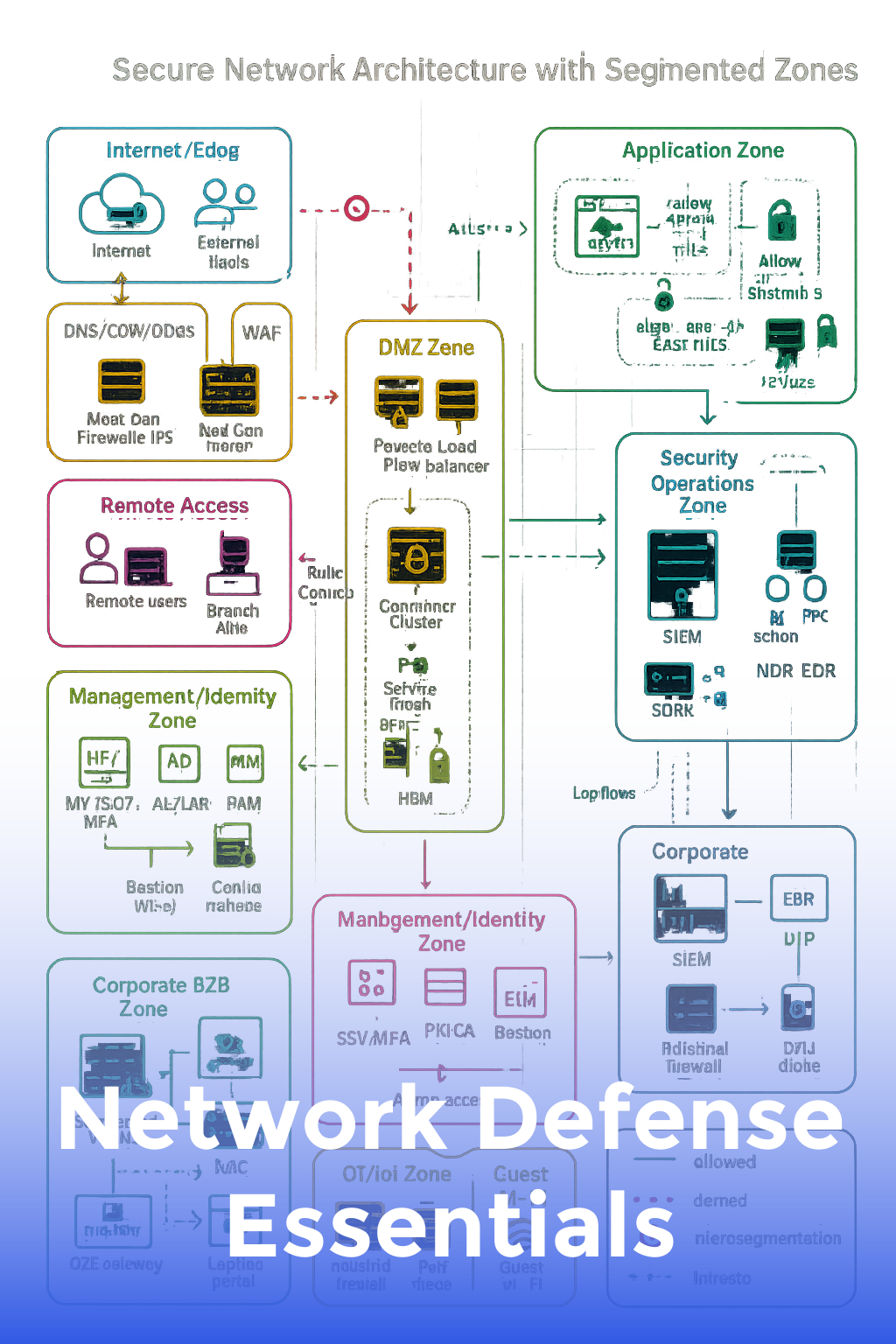
Network Defense Essentials
Configure firewalls, IDS/IPS, and network segmentation to block attacks.
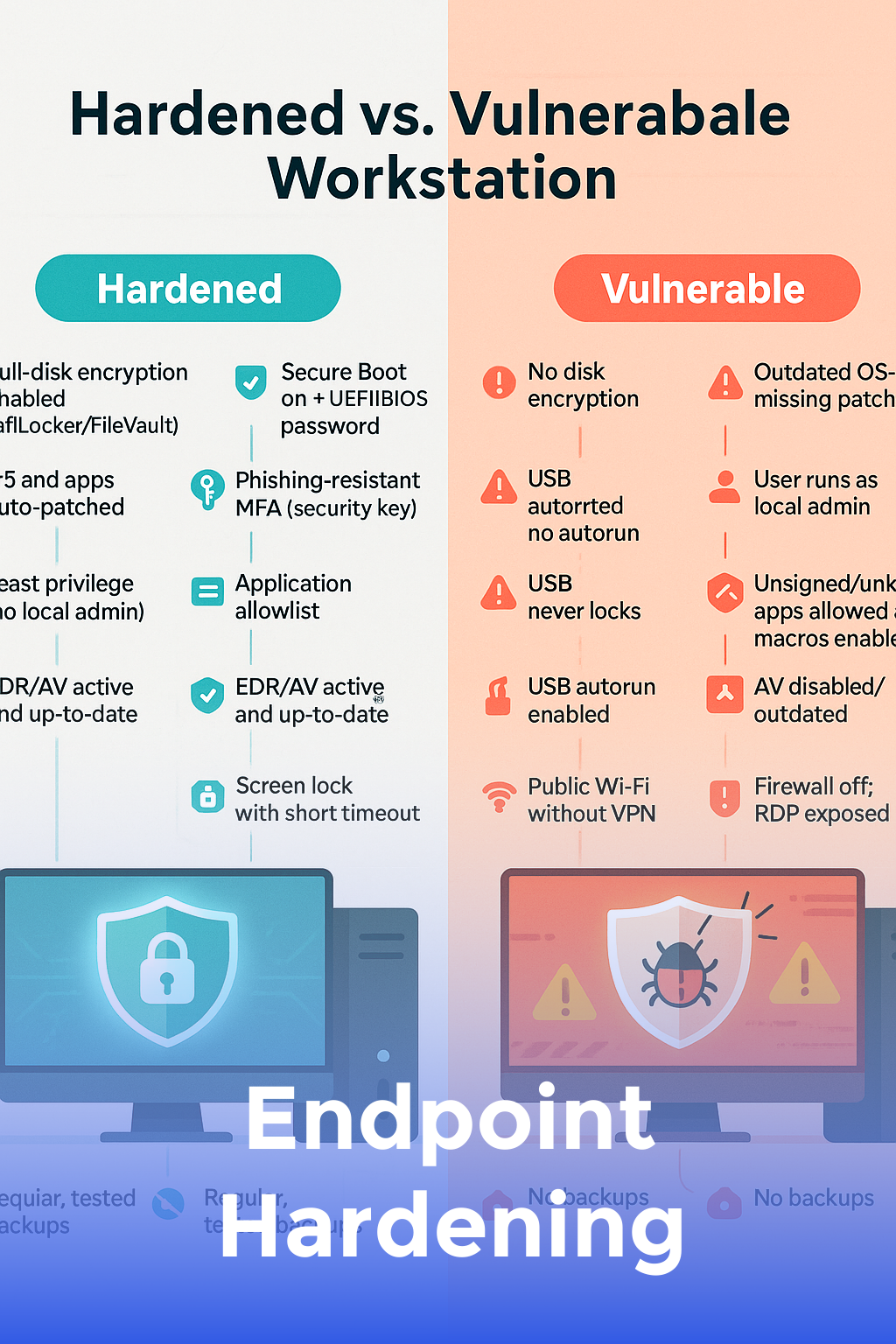
Endpoint Hardening
Implement patch management, EDR, and secure configurations on every endpoint.
Identity & Access Management
Apply least privilege, MFA, and role-based access controls across the enterprise.

Secure Application Practices
Spot and mitigate the OWASP Top 10 vulnerabilities in your applications.
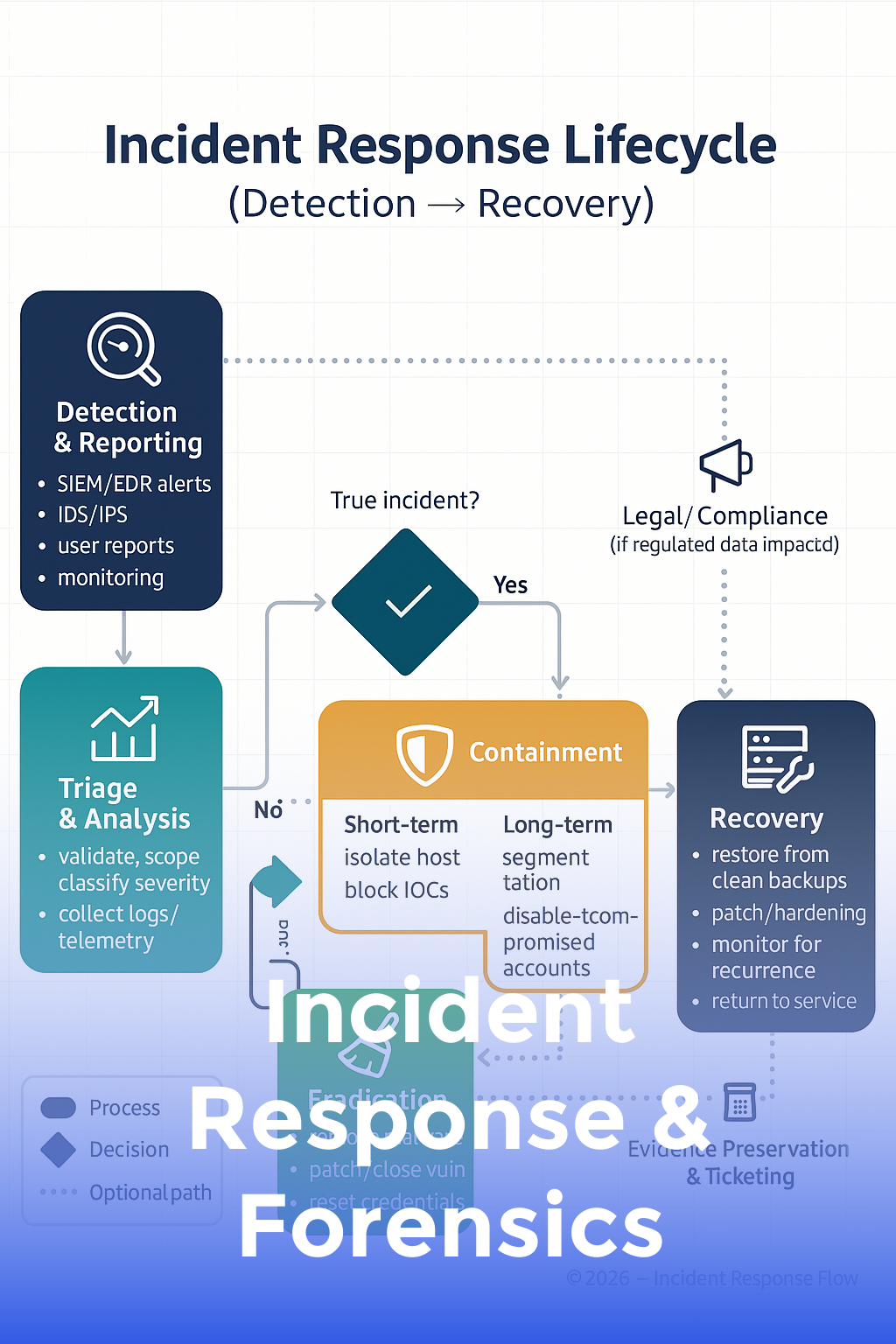
Incident Response & Forensics
Create playbooks, triage alerts, and collect evidence during incidents.
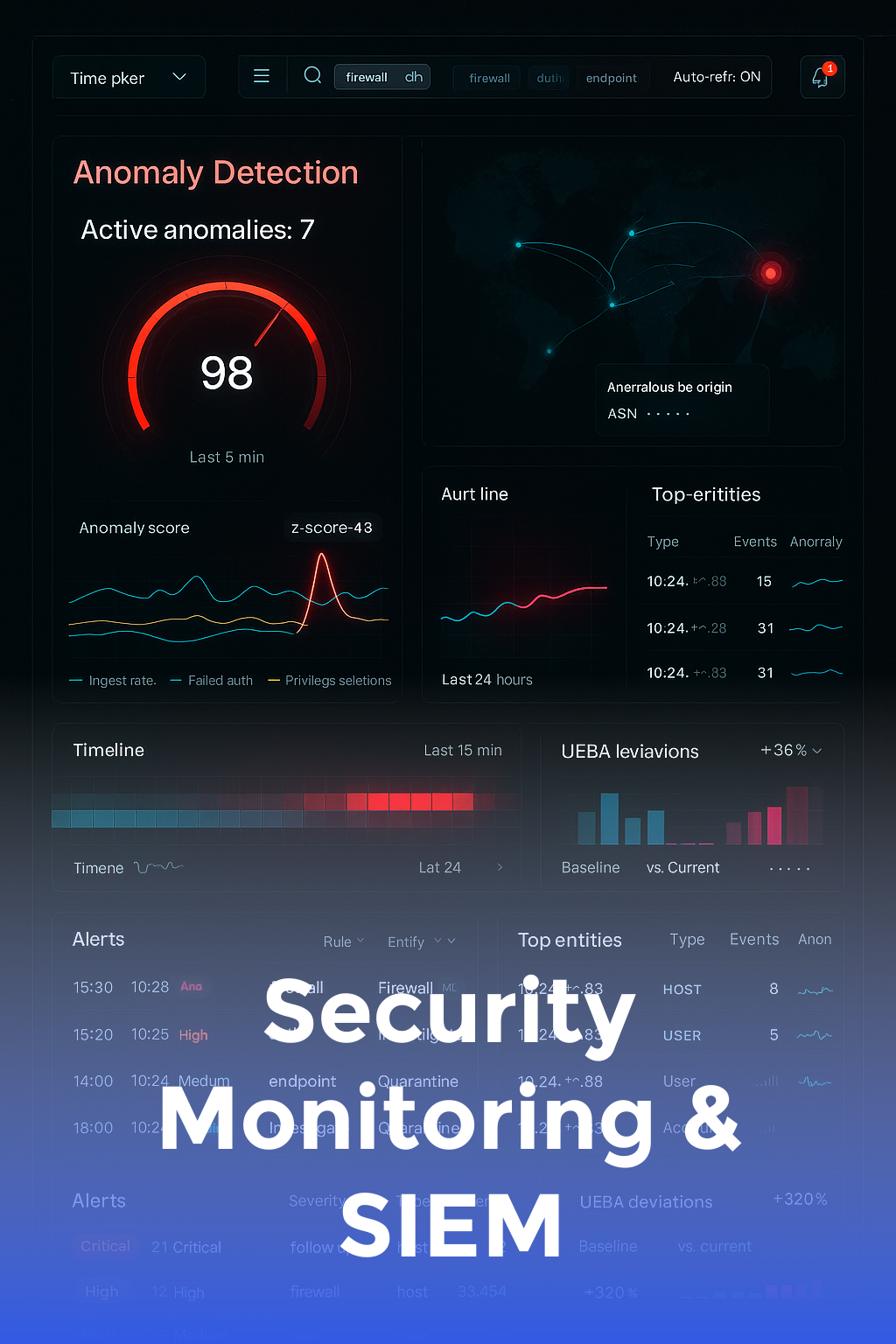
Security Monitoring & SIEM
Analyze logs, build SIEM dashboards, and tune alerts for actionable intelligence.

Building a Security Culture
Develop policies, conduct awareness training, and measure security maturity.

4.9/5 star reviews
Secure Your Organization from the Inside Out
A hands-on program that equips your team with practical skills to detect, prevent, and respond to cyber threats.
Here's what you get:
Instant access to 40+ HD training videos and interactive labs.
Downloadable security checklists, policy templates, and scripts.
Membership to a private Slack community for peer support and Q&A.
Lifetime updates aligned with emerging threats and new regulations.
Today Just
$997 one time

"Best purchase ever!"
" Our small team now confidently handles security incidents without outsourcing. The step-by-step labs made all the difference. "
ABOUT YOUR INSTRUCTOR
Meet Vince
Your instructor is a CISSP-certified security architect with two decades of experience defending Fortune 500 networks and mentoring security teams around the globe.
After leading dozens of breach investigations, he realized most incidents stemmed from fixable knowledge gaps—sparking his mission to create an actionable training that closes them.
Graduates have implemented robust security policies, passed industry certifications, and helped their companies avoid costly breaches—saving an average of $1.2M annually.
Former Chief Information Security Officer at a global tech firm.
Reduced breach containment time by 70% at a Fortune 100 company.
Trained over 5,000 professionals in cybersecurity best practices.
Keynote speaker at RSA, Black Hat, and SANS conferences.
Author of the bestseller "Practical Defense in Depth."
Honored by ISC² as Security Educator of the Year.

WHO IS THIS FOR...
IT staff, system administrators, and security-minded professionals seeking foundational and intermediate security skills.
System Administrators
IT Support Specialists
Network Engineers
DevOps Teams
Security Analysts
Compliance Officers
Small Business Owners
Students Pursuing Security Certifications
STILL NOT SURE?
Satisfaction guaranteed
We want you to find value in our trainings! We offer full refunds within 30 days. With all of our valuable video training, we are confident you WILL love it!

STILL GOT QUESTIONS?
Frequently Asked Questions
Does the course cover compliance standards?
Absolutely. Each module maps to frameworks like NIST CSF, ISO 27001, and PCI-DSS so you can meet regulatory requirements.
Do I need prior security experience?
No. We start with the basics and progress to intermediate topics. A general understanding of IT systems is helpful but not mandatory.
How is this course different from others?
We combine real breach case studies, interactive labs, and downloadable scripts so you can apply what you learn immediately—no fluff, just actionable skills.
Enroll in the course now!
Copyrights 2024 | Security Posture Pro™ | Terms & Conditions